What is SAP Cloud Connector (SCC)?
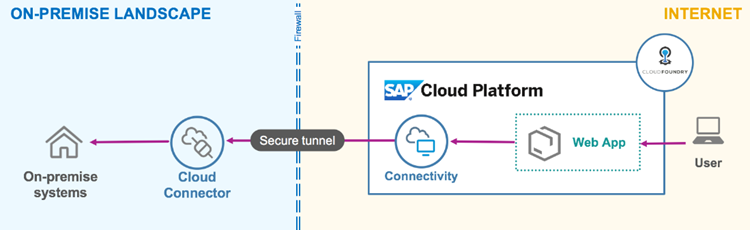
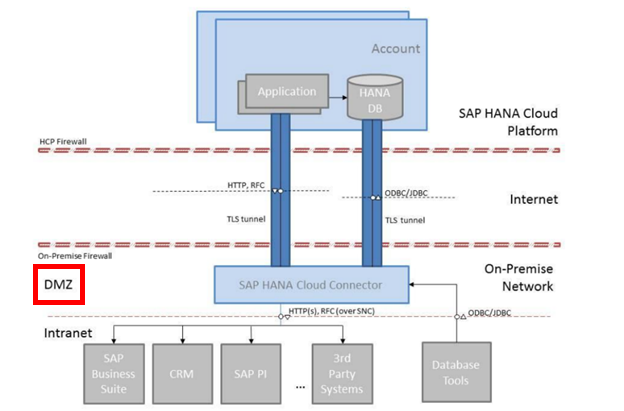
For connectivity und integration purposes from on-premise installations to the (SAP) Cloud, SAP developed a small piece of software called SAP Cloud Connector (SCC).
The SCC is the preferred method in customer (hybrid) environments to connect from on-premise to the (SAP) Cloud e.g., SAP Business Technology Platform (BTP), SuccessFactors and others; or generally to SAP Public Cloud Applications or SAP Private Cloud Applications.
Looking at the following chart, you will immediately realize that SCC becomes a center piece in regards to your (SAP) security posture.
Security Considerations for SAP Cloud Connector
There are several security areas we have seen during audits and when hardening the SAP Cloud Connector at our customers. Here are the “most wanted” areas to look out for:
- Patch-Management
- No High-Availability
- SCC location and setup in the network
- SCC built-in security features not used
- Usage of outdated Cypher Suites
- SCC Audit log not enabled or not monitored
1. Patch-Management
In 100% of all customer environments we have seen that the SCC itself or the related environments are not thoroughly patched. Recent research shows that 80% of cyberattacks happen due to unpatched software vulnerabilities.
We advise checking your implemented SCC version regularly and if it is not up to date you should consider upgrading your SCC to the latest version / patch-level as soon as possible.
Between 2013 and today there are many versions of SCC released and a lot of security patches related to SCC have been published by SAP too.
Now ask yourself: When was SCC initially implemented and how often have you implemented a new version or security patches since?
On top of that, please keep in mind that the underlying Operating System (OS) must be patched as well. Because SCC uses Java, the JVM or the SDK that is on your OS System is mandatory to be regularly patched too.
The effort to keep your SCC and its environment up to date is not very high, but you increase your security posture significantly!
Please check the SAP note 3302250 for details about the support strategy of the SAP Cloud Connector (3302250 – Cloud-Connector-Supportstrategie). It is worth mentioning because many customers do not know that security patches for SCC always apply exclusively to the latest available SCC version. Therefore, our strong recommendation is that customers always need to install the latest SCC version and patch to the latest patch-level available as soon as an SCC security patch becomes available. The lasted SCC version can be downloaded from https://tools.hana.ondemand.com/#cloud. Check the sections “Cloud Connector” and “SAP JVM”.
Watch out for the SAP Security Patch Day, every second Tuesday per month on SAP´s blog!
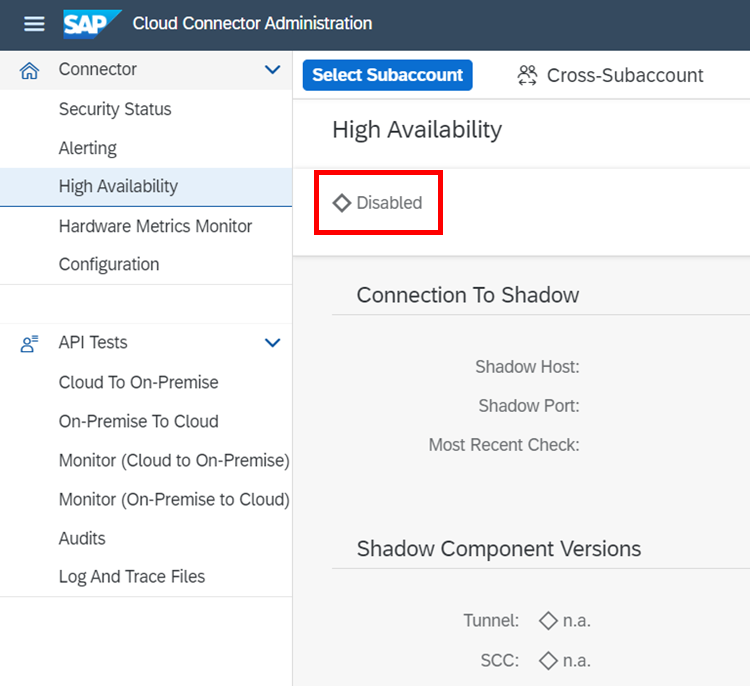
2. No High-Availability
Even though some think it is not a security feature, the SCC can be configured to make use of a High-Availability (HA) architecture.
Regarding the recommendation that the SCC needs new versions and regular patching it is vital to configure High-Availability to minimize the downtime and to avoid outages.
It is not particular for the SCC itself but for all applications sitting in the (SAP) Cloud that will be accessed by users through the SCC.
3. SCC location and setup in the network
We have seen SAP Cloud Connectors that are not located in the DMZ of the customers infrastructure. Even worse it happened, that there are not only official SCCs in the customer infrastructure which are perfectly located in the DMZ but also some test installations on Client PCs that are for test purposes. Obviously, those test installations are not maintained properly and been used aside w/o implemented security measures from the network team needed.
We also strongly recommend using a dedicated server especially for the SCC only to avoid that other administrators for other applications on the same server can access the SCC too.
Last but not least delete all unnecessary applications from the dedicated SCC server. We have seen game accounts on UNIX servers that must not be installed on an SCC environment. Make use of hard-drive encryption to make sure that the configuration and Audit Logs cannot be read by unauthorized users (Security Guidelines | SAP Help Portal). In >90% of all audits the hard-drive encryptions were not used.
4. SCC built-in security features not used
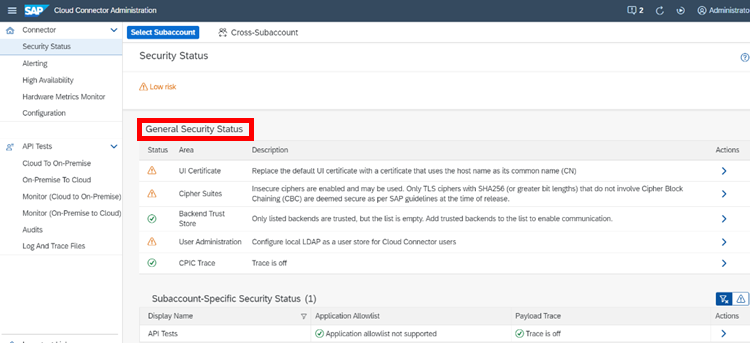
The SCC has a built-in security feature that allows customers to regularly check the security status of their SCC. In 93% of all SCC installations we have audited, the SCC security feature was either not known or not used by the customer.
The built-in security feature is the simplest way to raise your security posture to a mature level following the recommendations made. In the latest versions of SCC, the SCC can be connected and monitored through a standard API provided by SAP connecting to the solution manager.
If you have a SIEM system in place the API can also be used to integrate SCC into it, such as SAP Enterprise Threat Detection or others.
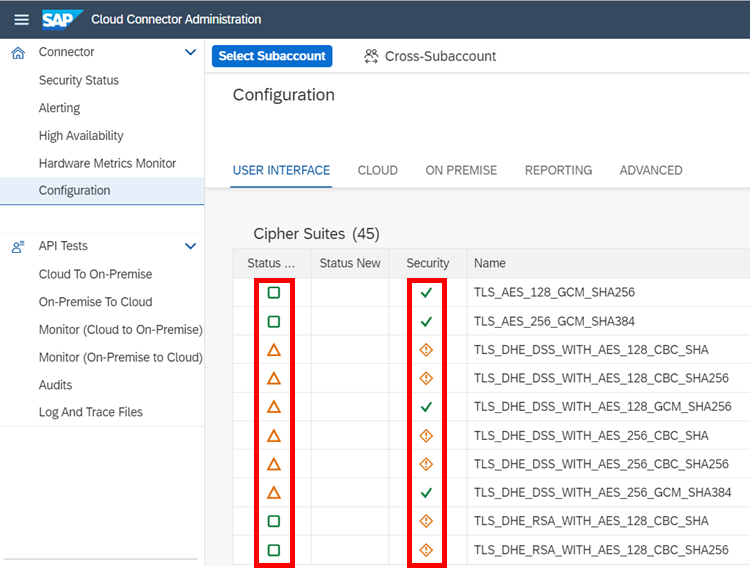
5. Usage of outdated Cypher Suites
In the past some Cypher Suites used by customers became obsolete or in some cases the encryption of some Cypher Suites is not secure anymore. SAP only allows a bit length of minimum 256 – all others deemed to be insecure. See OSS note: 2942602 – “Only TLS ciphers with SHA256 (or greater bit lengths) are deemed secure”.
We recommend using a bit length of 1024 minimum. Together with your security officer you should check the existing security policy to configure the cipher suite and bit length appropriately.
6. SCC Audit log not enabled or not monitored
The SCC has its own audit log that can be enabled for monitoring purposes. SAP lets you configure the audit level (subaccount or cross-sub-account). The default value is “Security” but can be extended to “All”. You must never use or configure “Off”.
There is also the option to choose the period of days how long you want to keep these logs using configuration field <automatic cleanup>.
As of SCC version 2.14 there is the possibility to also change the location of the audit log files. The files can be used to import into a SIEM system too.
For more details please check on SAP Help: Manage Audit Logs | SAP Help Portal.
Conclusion
The security topics for SAP Cloud Connector outlined in this article are meant for orientation and a first guidance. There are many more topics to look out for to make SAP Cloud Connector properly secure.
The most important message is that you cannot just implement a central SAP component like SAP Cloud Connector and keep it at a low maintenance level. It is essential that you integrate SAP Cloud Connector in your software lifecycle management and keep high attention like it would be your main SAP ERP system, especially when it comes to security.
Related topics: smarterSec Security Platform // Managed Security Service for the smarterSec Security Platform