CVE-2021-44228 – log4shell
(Updated: 12/16/2021)
The open-source Java library log4j provides common services for creating and managing application logs and is widely used as part of Apache Software Foundation (https://logging.apache.org/).
The vulnerability, known as “log4shell”, allows remote code execution (RCE), i.e. the reloading and execution of source code. Exploitation of the vulnerability is relatively simple and can be achieved by attackers adding technical commands to their input, which are written to the log and interpreted.
The vulnerability, officially marked as CVE-2021-44228 [1], has been given a CVSS Base Score of 10.0, which is the highest rating. The BSI also shares this opinion and has changed the IT threat level to 4/red: [2].
General comments on mitigation
- The fix to close the vulnerability requires an update of the log4j library to version 2.16.0. Addition: after initially recommending the upgrade to log4j 2.15.0, this fix turned out to be insufficient and had to be extended again.
- This change of the library can typically only be done when it comes to customer specific solutions. For standard software (or add-ons to it), the patch must be provided by the manufacturer.
- As an alternative mitigation, Apache recommends removing the affected class JndiLookup.class from the log4j.jar archive since 12/15/2021. On the log4j-Security homepage [3] corresponding instructions are described, which however must be adapted to the own application. Attention: this measure requires an appropriate test since the logging functionality is modified by this.
- The previously described mitigation by setting program parameters (-Dlog4j2.formatMsgNoLookups=True) or system environment variables (LOG4J_FORMAT_MSG_NO_LOOKUPS=True) is now listed as “discredited”, i.e. the attack vector is reduced, but not completely closed.
- The BSI provides more details here in an advisory [4].
Context SAP applications
The SAP instructions known so far can be viewed here [5]. Alternatively, they can be searched and downloaded via the SAP Service Marketplace. The screenshot shows an overview of the advisories as of 12/14/2021.
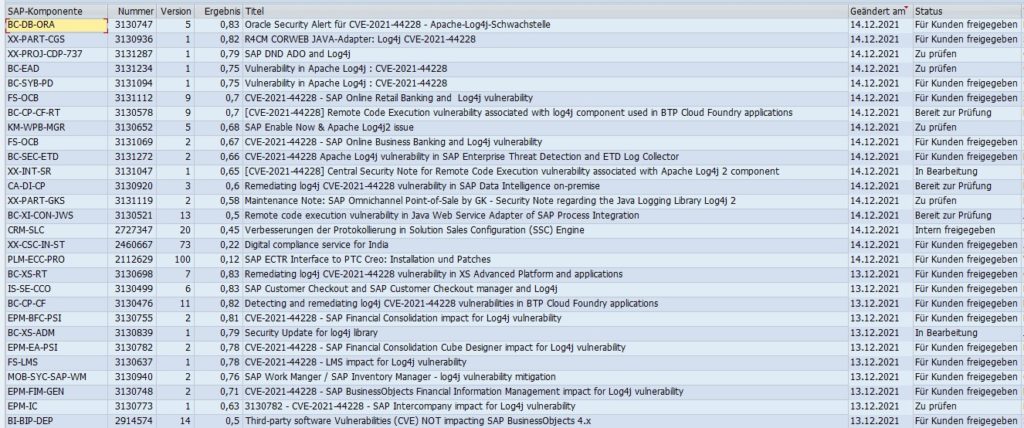
- We recommend analyzing all notes from the above-mentioned source and checking whether they can be implemented. Importable fixes should be implemented urgently (according to the customer’s HotFix/Emergency Transport process).
- In addition, the new SAP notes for further corrections against log4shell should be checked regularly in the next days.
In the context of SAP Add-Ons
If an affected release of the log4j library is used in the add-on, it usually cannot be replaced directly by the end user. As with SAP, many add-on vendors have already provided corresponding patches (or will do so in the near future).
- We strongly recommend to apply corrections provided by the manufacturer immediately.
- As described above – until a patch is delivered – the critical functionality from log4j can be disabled via configuration. However, since this changes the functionality of the log, we recommend to do this only after consultation or on a corresponding advisory/recommendation from the manufacturer.
- If such a recommendation from the vendor is not yet available, we recommend creating a corresponding customer message / support ticket and asking for the status of the add-on regarding the log4shell vulnerability.
References
[1] Mitre: CVE-2021-44228 https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2021-44228
[2] BSI: Critical “Log4Shell” vulnerability in widely used logging library Log4j (CVE-2021-44228) https://www.bsi.bund.de/SharedDocs/Cybersicherheitswarnungen/DE/2021/2021-549177-1032.pdf?__blob=publicationFile&v=2
[3] Apache: log4j Security page https://logging.apache.org/log4j/2.x/security.html#CVE-2021-44228
[4] BSI: Critical vulnerability in Log4j CVE-2021-44228 Detection and Response Working Paper https://www.bsi.bund.de/SharedDocs/Downloads/DE/BSI/Cyber-Sicherheit/Vorfaelle/log4j-Schwachstelle-2021/log4j_Schwachstelle_Detektion_Reaktion.pdf?__blob=publicationFile&v=2
[5] Overview of affected vendors and applications, list of SAP notes https://gist.github.com/SwitHak/b66db3a06c2955a9cb71a8718970c592#gistcomment-3994039